Data Pulse Start 816-643-2731 Revealing Trusted Phone Signals

Data Pulse Start 816-643-2731 integrates encryption, PKI, and real-time scoring to verify caller legitimacy. The system decodes signal patterns, cross-references subscriber data, and applies device attestations to present trusted status. Privacy protections emphasize opt-in controls and minimal data sharing, with clear disclosures and proactive alerts. This framework aims for accountable, risk-aware routing while balancing user autonomy with governance. It raises a question: how reliably can such signals distinguish legitimate calls in practice, and what are the trade-offs?
What Are Trusted Phone Signals and Why They Matter
Trusted phone signals refer to verifiable indicators that a phone number or communication is legitimate and secure.
The analysis identifies trusted signals as benchmarks of authenticity, reducing uncertainty in outreach and maximizing autonomy.
Privacy safeguards described as core requirements, alongside satisfied calls, reinforce accountability.
Caller identity remains central, guiding trusted interactions while enabling individuals to discern genuine intent from deception.
How Modern Carriers Verify Caller Authenticity
Modern carriers employ a multi-layered verification framework to authenticate caller identity, combining signaling analysis, database lookups, and device-based attestations. This approach aims to validate trusted caller status while evaluating phone signals integrity.
Realtime checks cross-reference subscriber records with anomaly alerts, reducing spoof attempts. Results influence call routing and presentation, balancing user freedom with accountability, and preserving trust in telecommunications ecosystems.
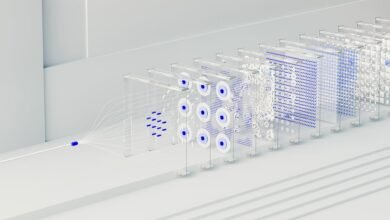
Decoding Signal Patterns: Encryption, PKI, and Real-Time Scoring
Linking verification practices to signal integrity, the discussion turns to how encryption, PKI, and real-time scoring decode and secure call patterns. Decoding patterns reveal encryption verification methods, enabling robust caller authentication while preserving user autonomy. Real time scoring assesses trust signals, thresholds, and anomaly flags, guiding risk-aware routing. The approach remains precise, analytical, and freedom-oriented, emphasizing transparent, enforceable standards without compromising privacy.
Practical Ways to Recognize Legitimate Calls and Protect Privacy
In practice, call verification hinges on cryptographic attestation, trusted caller IDs, and real-time risk indicators.
Privacy protection requires minimal data sharing, opt-in controls, and clear disclosure.
Audiences seeking freedom value transparent filtering, proactive alerts, and consistent enforcement of personal data governance.
Conclusion
In summary, trusted phone signals blend encryption, PKI, and real-time scoring to verify caller legitimacy while preserving privacy. Carriers harness device attestations and subscriber data cross-checks to reduce uncertainty in outreach and guide risk-aware routing. The framework emphasizes opt-in controls, clear disclosures, and proactive alerts, fostering accountability. Yet, as signals mature, the balance between security and privacy remains a delicate tightrope—a lighthouse in fog, directing decisions without surrendering user autonomy.