Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
The discussion on Account Data Review for the listed identifiers will emphasize precision, privacy, and governance. It outlines structured data quality checks, risk-aware controls, and traceable change logs while preventing exposure of raw identifiers. The approach favors minimization and hashed validation, with clear lineage and incident response readiness. Safeguards and periodic risk reviews form the backbone of ongoing stewardship. A conservative, methodical path awaits, inviting stakeholders to consider how to sustain operational integrity without compromising confidentiality.
What a Safe Account Data Review Entails
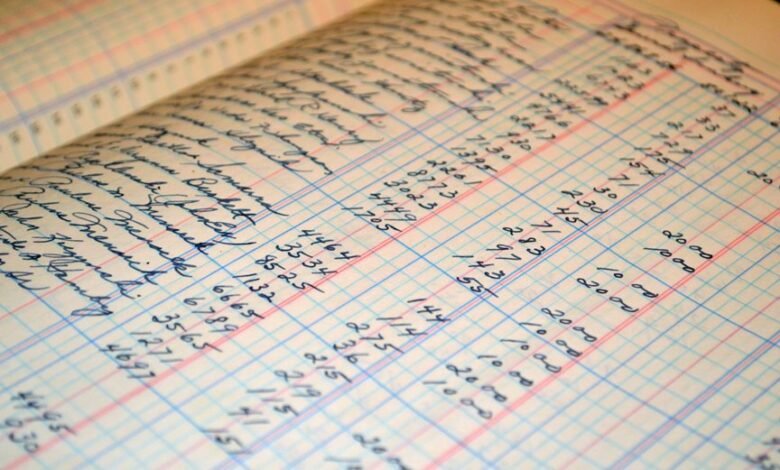
A safe account data review entails a structured, methodical examination of all relevant data elements to ensure accuracy, completeness, and appropriate access controls.
The assessment emphasizes privacy auditing and data governance, detailing risk framing, role-based permissions, and traceable change logs.
It remains detached, precise, and vigilant, advocating freedom through transparent governance, consistent remediation, and documented accountability without unnecessary speculation or ambiguity.
Key Data Quality Checks You Should Perform
Key data quality checks are essential to validate accuracy, completeness, and consistency across data assets. The analysis emphasizes systematic data quality, with emphasis on transparency and traceability. It supports disciplined risk assessment by identifying anomalies, gaps, and duplications. Practitioners apply quality metrics, lineage, and validation rules to sustain reliable insights while maintaining freedom to innovate within governance constraints.
How to Validate Identifiers Without Exposure
How can identifiers be validated without exposing sensitive details? The process emphasizes identity validation while prioritizing data minimization. Operators compare cryptographic proofs or hashed identifiers, avoiding raw data exposure. Auditors verify consistency through anonymized tokens and secure identity attestations. This disciplined approach preserves user control, reduces risk, and supports transparent governance. Precision, discipline, and deliberate restraint underpin reliable, privacy-conscious validation without unnecessary data disclosure.
Implementing Safeguards and Next Steps for Ongoing Review
Implementing safeguards and planning next steps for ongoing review requires a structured framework that reinforces privacy by design while sustaining operational integrity.
The safeguards overview emphasizes layered checks, access controls, and audit trails.
Ongoing review steps include periodic risk assessments, data minimization, and incident response drills.
Documentation remains concise, decisions traceable, and governance transparent, aligning freedom with responsible data stewardship.
Frequently Asked Questions
How Often Should Reviews Be Conducted for Account Data?
How often, account reviews should occur regularly; stakeholders approve the cadence after reviewing results. The precise schedule is established to ensure ongoing data integrity, security, and transparency, reflecting diligent, meticulous governance while preserving stakeholders’ freedom to adapt as needed.
Which Stakeholders Must Approve the Review Results?
Stakeholder approvals come from the data owner, compliance, and IT governance bodies, with clear sign-off on data access documentation. The review results require documented consent, traceable accountability, and formal authorization before proceeding.
What Are Common False Positives to Watch For?
Common false positives arise when automated checks misclassify benign activity, potentially compromising account data integrity; diligent reviewers correlate context, thresholds, and provenance to prevent mislabeling while preserving user autonomy and data quality.
How Should Data Access Be Documented During Reviews?
Data access should be documented with rigorous adherence to documentation standards, detailing user roles, timestamps, approvals, and scope; records must be legible, auditable, and stored securely, supporting transparent yet disciplined review without compromising freedom.
Can Review Findings Impact Customer Privacy Policies?
Review findings can influence privacy policies, revealing privacy implications and driving updates to data retention practices. The process underscores cautious, transparent procedures, balancing freedom with accountability, ensuring sensitive data handling aligns with evolving regulatory expectations and organizational risk tolerance.
Conclusion
The audit concludes that privacy-preserving practices, coupled with rigorous validation and governance, sustain trustworthy account data stewardship. By applying data minimization, hashed validations, and transparent change logs, the review minimizes exposure while preserving traceability. Comprehensive quality checks, lineage tracing, and defined incident response readiness reinforce operational integrity. Ongoing risk assessments and periodic governance alignment ensure sustained compliance. Stakeholders can proceed with confidence, knowing safeguards are in place to weather any storm, and the framework remains airtight. outcomes stand firm.




