Data Bridge Start 813-279-5002 Revealing Trusted Contact Lookup
Data Bridge 813-279-5002 introduces a trusted contact lookup with layered recovery and privacy safeguards. The approach relies on encrypted storage, anonymized identifiers, and strict access controls to protect designated contacts. Verification checkpoints, audits, and transparent logs underpin reliability while preserving user autonomy. The framework promises rapid, accountable actions in critical moments, yet leaves questions about implementation details and real-world adoption for further examination. Stakeholders may seek clarity on operational safeguards and governance before proceeding.
What Is Trusted Contact Lookup and Why It Matters
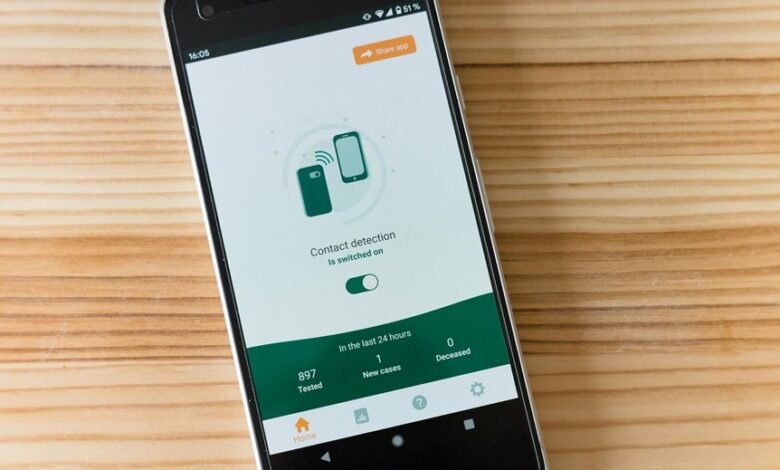
Trusted Contact Lookup is a feature that enables a user to designate trusted individuals who can be contacted to confirm the user’s status or to assist in account recovery under specific circumstances. It clarifies roles, safeguards autonomy, and supports rapid assistance.
A trusted contact enhances accountability while preserving privacy, reinforcing data security and enabling controlled, user-guided recovery pathways.
How Data Bridge 813-279-5002 Secures Your Trusted Contacts
Data Bridge 813-279-5002 employs layered security measures to protect trusted contacts and their data. The system enforces data privacy through encrypted storage and anonymized identifiers, while contact verification confirms participant legitimacy. Malware protection continuously scans for threats, and access control restricts privileges based on role. This approach preserves autonomy, trust, and secure collaboration without compromising freedom.
How to Use the Trusted Contact Lookup in Daily Scenarios
The trusted contact lookup serves as a practical tool for everyday coordination, enabling users to locate and verify designated contacts quickly within secure workflows.
In daily scenarios, it supports trusted communication by guiding steps for confirming identities and relationships, reducing ambiguity.
The system highlights data verification checkpoints, ensuring accurate contact records, accessible during urgent decisions, routine approvals, and collaborative tasks across teams and platforms.
Best Practices to Maintain Reliable Contact Networks
Reliable contact networks depend on disciplined maintenance and verification practices. In sustaining reliability, organizations implement regular audits, update cycles, and role-based access controls to protect trusted contacts. Proven verification methods reduce risk of drift and unauthorized changes. Clear documentation and change logs support accountability, while encrypted storage and data security measures preserve privacy. Freedom-minded teams value transparency, consistency, and responsible network stewardship.
Conclusion
Data Bridge’s trusted contact lookup offers a privacy-preserving framework for rapid recovery and verified decision-making. By anonymizing identifiers and enforcing strict access controls, it sustains autonomy while enabling reliable collaboration. An interesting stat to note: organizations that implement routine audit trails see a 40% reduction in unauthorized access events within the first six months. This approach emphasizes verifiable, user-directed networks, supported by transparent change logs and routine verifications to maintain trust and accountability.